Add Cloud Visibility to Your Attack Surface Management Program
The external attack surface expands beyond DNS and domains to include resources and applications hosted in the cloud. For organizations with footprints on-prem and in two or more cloud environments, achieving continuous and centralized visibility of all owned assets is cumbersome, leading security teams to toggle between consoles to cobble together a view of the attack surface.
Adding to the challenge, the acceleration of cloud adoption has yielded an increasing number of applications entering cloud instances before the security team can assess them for risk. Real-world observations indicate that threat actors target external-facing applications for initial compromise; to strengthen defenses, security teams must establish visibility into the entire ecosystem.
We’re excited to announce Mandiant Attack Surface Management for Google Cloud, the latest integration that enables customers to extend visibility into assets across multi or hybrid cloud environments. When used to automatically discover assets from multiple cloud providers, DNS and the extended external attack surface, customers gain a deeper understanding of their ecosystem and the insights to better prioritize remediation on the vulnerabilities and exposures that present the most risk.
Expand Visibility with Automated Asset Discovery
When it comes to prioritizing attack surface risks, the first step is establishing a baseline of the external asset inventory to understand where the assets in the ecosystem live and who owns them. From there, monitoring for changes or unknowns in the environment becomes easier. Automating asset discovery from various clouds, DNS providers and on-prem saves the security team precious time.
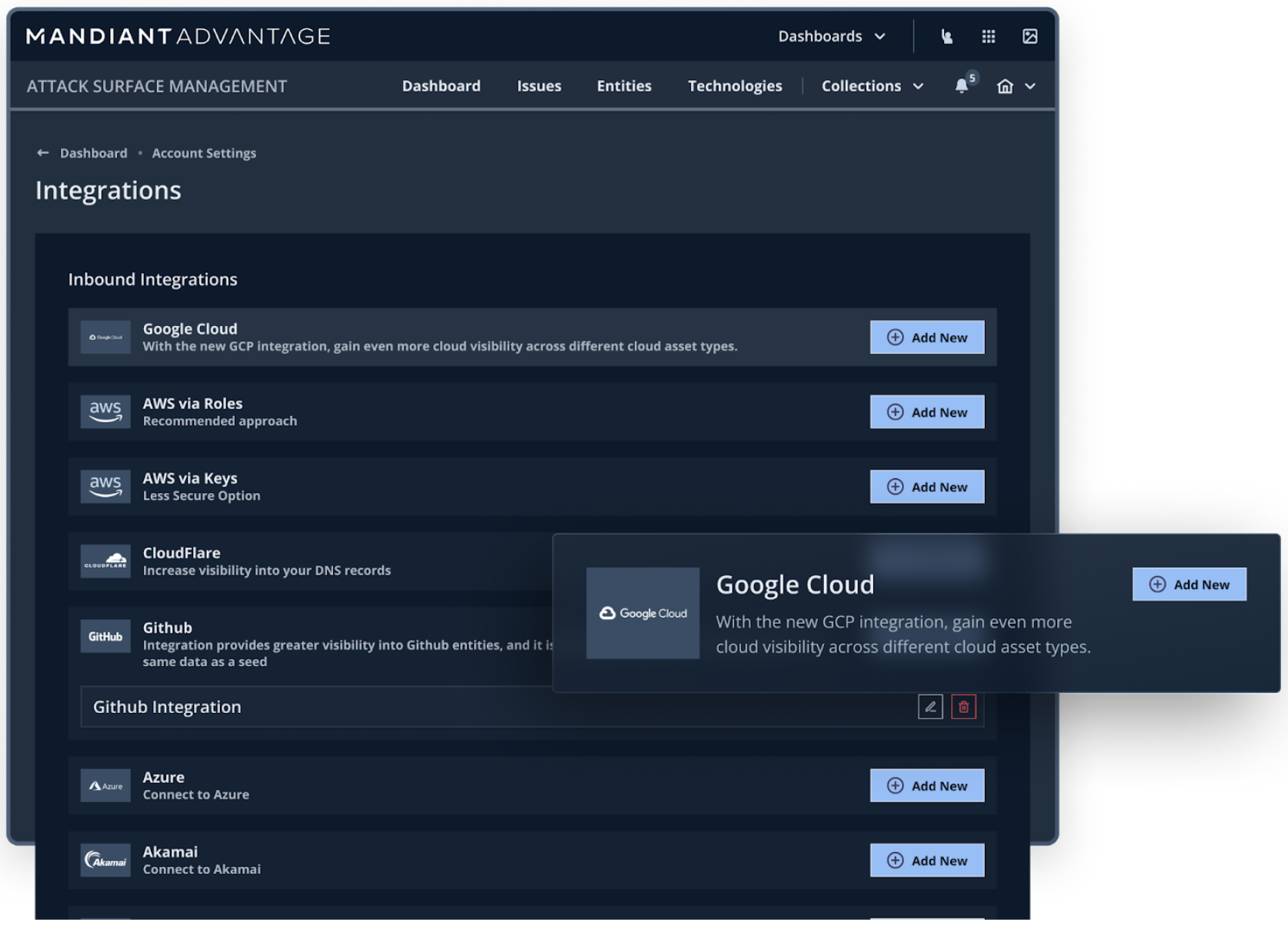
Mandiant Attack Surface Management uses APIs to retrieve assets from AWS, Azure, Akamai DNS Edge, Cloudflare, GoDaddy, GitHub and now Google Cloud to streamline discovery and enumeration, and deliver a centralized view of the external attack surface.
With a consolidated view of external assets, security teams can answer critical questions when it matters most. Take a situation like Log4j for example, where executive stakeholders want the answers to: “What is the breadth of the impact of the latest vulnerability?” and, “What is our plan for remediation?” Customers can easily search through the technology inventory to determine which external assets are impacted.
Intelligent Prioritization
Attack Surface Management actively checks assets for vulnerabilities, misconfigurations and exposures assigning a severity to security issues identified on assets after enriching the attack surface findings with Mandiant Threat Intelligence. For example, a Google Cloud asset like an internet-accessible storage bucket used to host static marketing resources may receive a low severity issue, while an exposed MySQL database may receive a medium severity alert. In both scenarios, the security team needs to be aware of the exposures and should act to validate or fix the configurations, and initiate incident response if necessary.
Overlaying threat intelligence onto external assets allows Attack Surface Management to account for CVE exploitation status and the existence of an exploit code in the severity assignment. Customers can configure security issue generation to align with their specific cyber risk threshold and the volume of security issues the security team can handle.
Act on Insights
Knowing about security issues is only half the battle. Mandiant strongly recommends that insights from the attack surface be leveraged within a security operations workflow. Operationalizing insights can take many forms. Attack Surface Management customers leverage the available API and integrations to automate the following:
- Expanding the asset scope within the vulnerability management tool
- Contextualizing security operations investigations on external exposures
- Prioritizing external security issues within workflows based in Splunk, ServiceNow, or Jira
- Updating compliance risk assessments with information on shared assets, subsidiaries, and digital suppliers
Assess your multicloud attack surface; contact us to request a trial of Mandiant Attack Surface Management.
