
Resources
Threat Intelligence Reports
Threat Intelligence from front line experts.

report
The Defender’s Advantage Cyber Snapshot, Issue 5
Nov 15, 2023 1 min read
report
FIN12 GROUP PROFILE: FIN12 PRIORITIZES SPEED TO DEPLOY RANSOMWARE AGAINST HIGH-VALUE TARGETS
Nov 13, 2023 1 min read
solution brief
Integrated Reasoning™
Nov 10, 2023 1 min read
report
Google Cloud Cybersecurity Forecast 2024
Nov 08, 2023 1 min read
solution brief
Virtual CISO (vCISO) and CISO Advisory Services
Nov 06, 2023 1 min read
solution brief
Virtual CISO (vCISO) and CISO Advisory Services
Sep 14, 2023 1 min read
report
The Defender’s Advantage Cyber Snapshot, Issue 4
Sep 05, 2023 1 min read
report
The Forrester Wave™: External Threat Intelligence Service Providers, Q3 2023
Jun 30, 2023 1 min read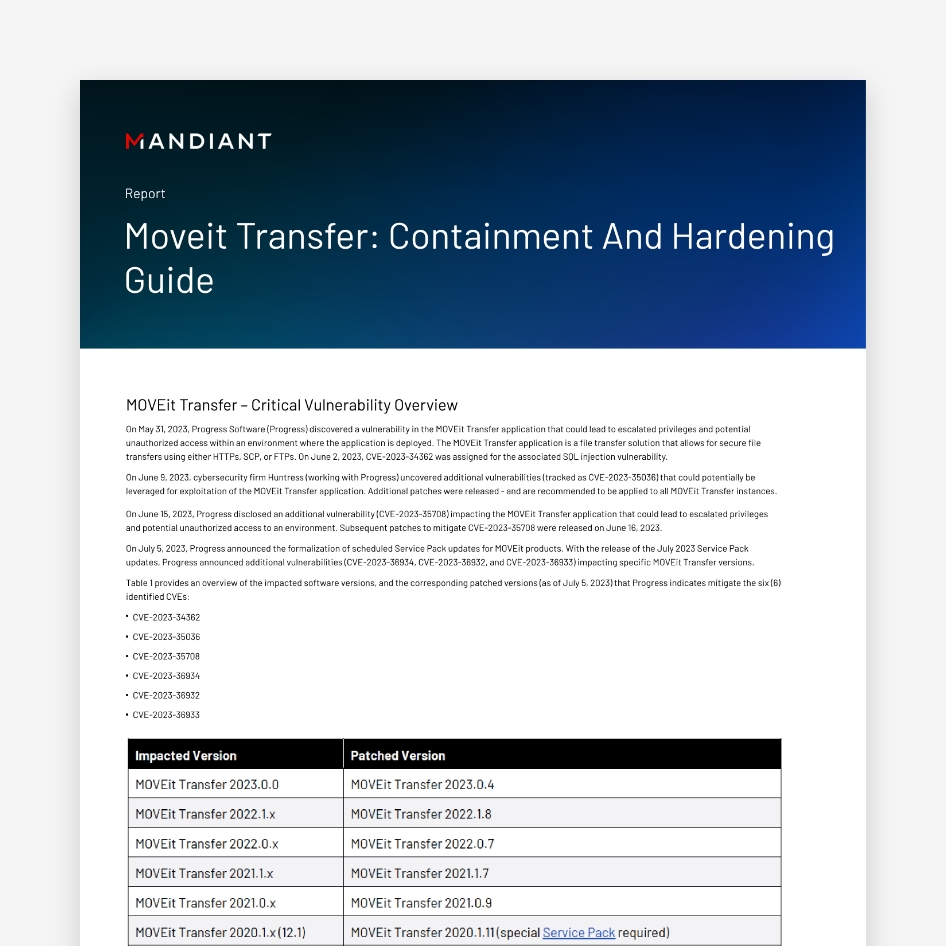
report
MOVEit Transfer: Containment and Hardening Guide
Jun 27, 2023 1 min read
M-Trends 2023
Insights into Today's Top Cyber Trends and Attacks
Mandiant's annual report provides an inside look at the evolving cyber threat landscape. Explore threat intelligence analysis of global incident response investigations, high-impact attacks, and remediation.