Stolen Credentials Make You Question Who Really Has Access
Are your passwords floating around on the dark web? How would you know if they were? It’s more important than ever to be proactive in protecting your organization's data. One of the best ways to do this is to monitor for credential leaks.
A credential leak occurs when sensitive information, such as usernames, passwords, and API keys, is exposed to the public. This can happen in any number of ways, including data breaches, phishing attacks, credential stealers, and social engineering. Once credentials are leaked, they can be used by attackers to gain unauthorized access to your organization's systems and data. This can lead to data theft, financial losses, and reputational damage. By monitoring for credential leaks, you can identify compromised credentials early on and take steps to mitigate the risk of an attack.
The Benefits of Credential Leak Monitoring
There are a number of benefits to implementing credential leak monitoring, including:
- Reduced risk of data breaches: Credential leak monitoring can help you identify compromised credentials early on, which can reduce the risk of a data breach.
- Improved security posture: Credential leak monitoring can help you improve your organization's security posture by identifying and addressing vulnerabilities.
- Increased compliance: Credential leak monitoring can help you demonstrate compliance with industry regulations, such as GDPR and PCI DSS.
- Cost savings: Credential leak monitoring can help you save money by reducing the cost of data breaches and other security incidents.
The Cost of Not Addressing the Problem
According to the M-Trends 2023 report, stolen credentials are the third most used infection vector behind exploits and phishing. Data breaches can result in severe financial losses for organizations. According to a survey by Constella Intelligence, a staggering 53% of cybersecurity executives reported data breach costs ranging from $100,000 to $1 million. In the enterprise sector, the average breach burden stands at a daunting $4.2 million. This underscores the need for rapid identification of compromised credentials as an essential skill for security operations (SecOps) teams.
Strikingly, even though over half of executives surveyed acknowledged multiple instances of leaked credentials for key employees in the past two years, nearly half admitted to not actively monitoring for leaked credentials on the dark web.
Start Monitoring Today
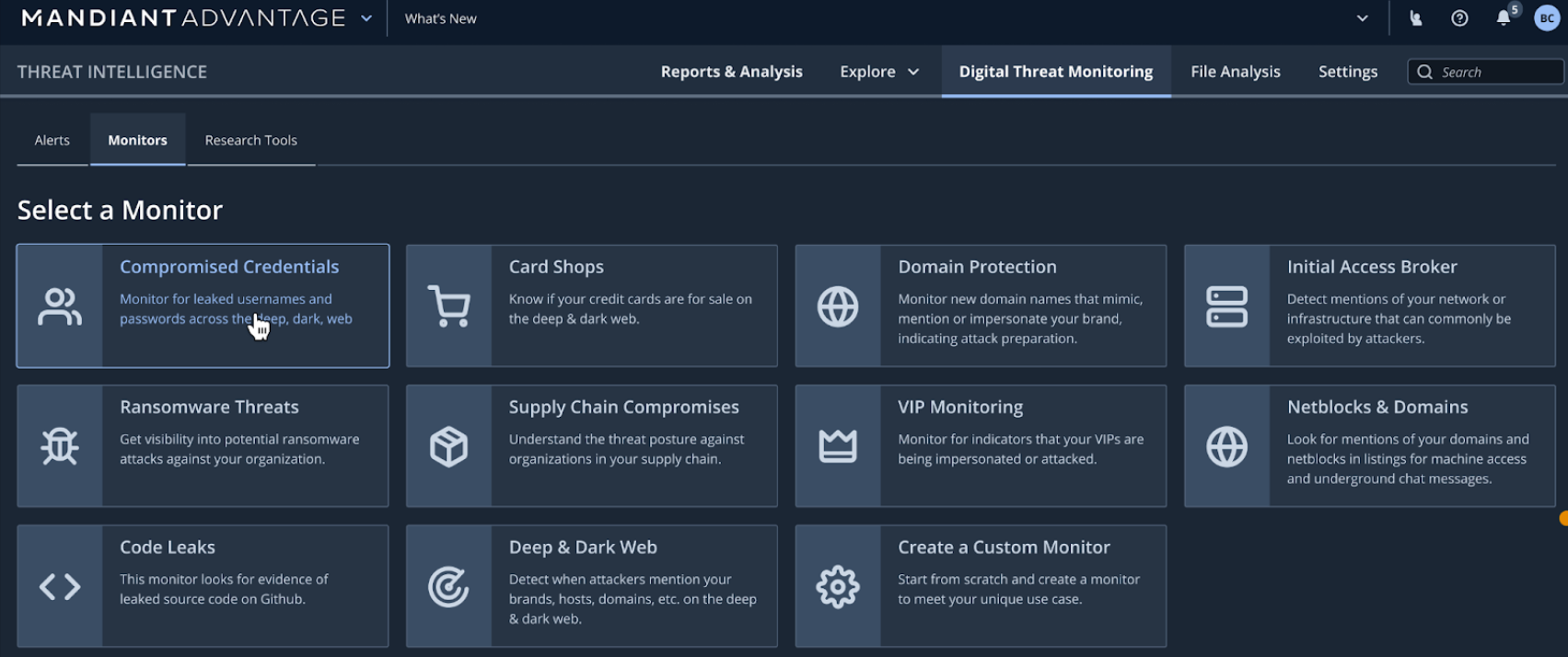
Mandiant Digital Threat Monitoring now includes the capability to monitor your credential leaks on the deep and dark web. To simplify the setup process there is an easy-to-use template, and in just a few steps you can start monitoring your exposure. The credential leak monitoring capabilities in Digital Threat Monitoring will automatically alert you if your employees’ accounts have appeared in our compromised credential data. By monitoring for credential leaks and taking action on the alerts, you will be able to promptly reduce the window of exposure, preventing account takeovers, and minimizing the potential impact on your threat landscape.
Credential leak monitoring is an important security measure that can help you protect your organization from data breaches and other security incidents. By monitoring for leaked credentials, you can take a proactive step towards protecting your employees, customers, and your business reputation from ever-present threats.
