![]()
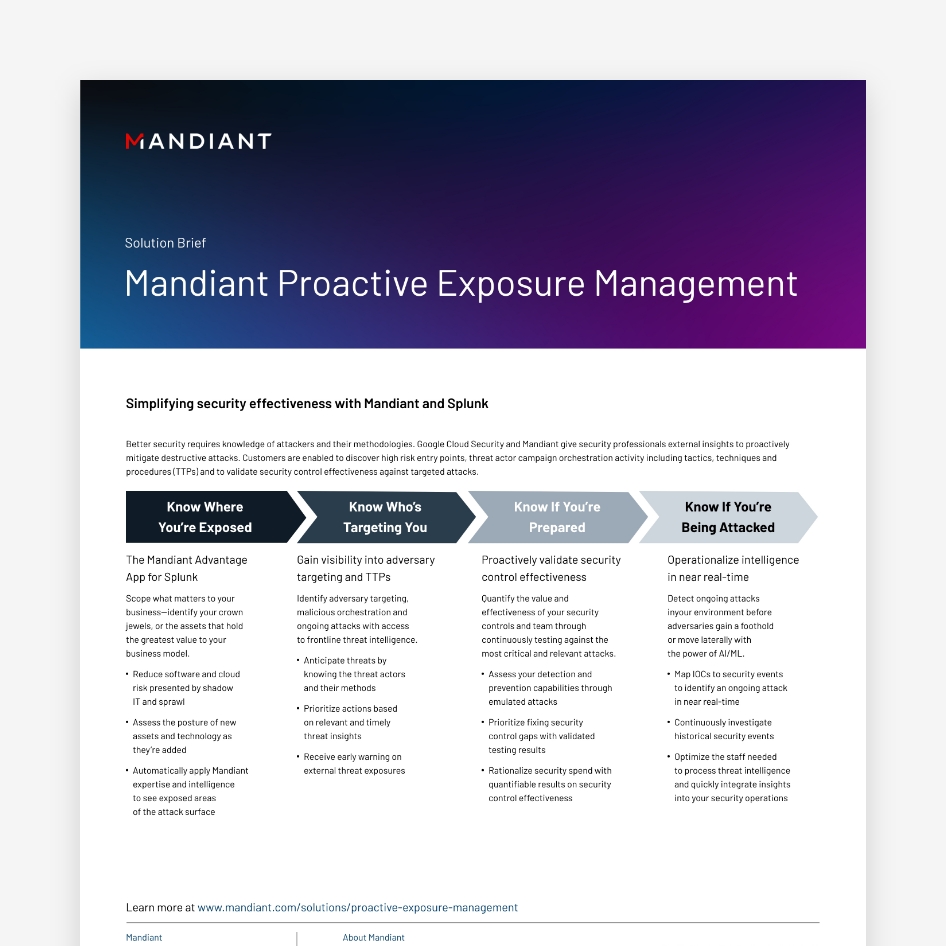
Reduce Unknowns
Identify unknown assets, malicious orchestration, and ongoing compromise
![]()
Harden the Attack Surface
Prioritize patching and hardening efforts for exposures with the highest potential impact
![]()
Defend Crown Jewels
Ensure your approach to cyber defense is built to combat targeted attacks
![]()
Identify Risk During M&A
Identify and assess existing risk that is outside of your control
![]()
Monitor Subsidiaries
Continuously monitor your entire portfolio for vulnerabilities and malicious adversary targeting

Security Leader’s Guide to Exposure Management
Go beyond vulnerability patching to full exposure mitigation. Learn how to establish an exposure management program within your cyber defense organization.
Identify exposures before an incident
Security teams need tools that can see into the digital expanse: into SaaS applications, IaaS and cloud-based environments, along with apps, systems and third-party data across the digital supply chain. A comprehensive attack surface management approach maps external assets and supply chain dependencies, while operationalizing attack intelligence to develop a proactive security program.
Exploits are the #1 initial infection vector in incident response investigations.
Source: M-Trends 2023
17%of breaches had the supply chain identified as the initial infection vector--the second most common initial infection vector—this highlights the need to continuously monitor partner security posture.
Source: M-Trends 2022
Frequently asked Questions
Examples of attack surfaces include domains, IP ranges, data repositories, websites, servers, email, cloud resources, applications, microservices and employees.
Getting Started
Mandiant experts are ready to answer your questions. Contact Mandiant to learn more about exposure management and how to advance your cyber security posture.