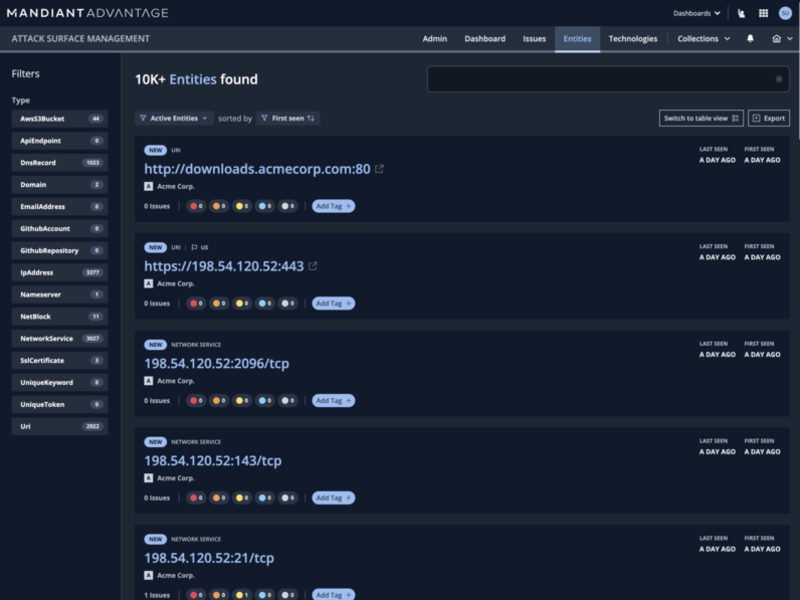
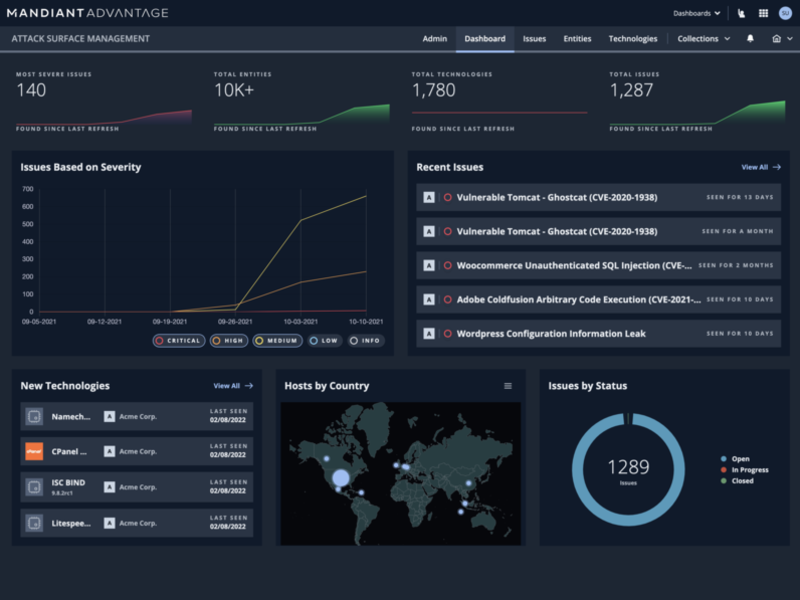
Broad asset visibility across your entire external ecosystem
Attack Surface Management empowers digital innovation
Comprehensive asset discovery and risk mitigation help enable safe adoption of new technology and processes that speed innovation. You can better protect your perimeter and become more competitive.
- Support remote hybrid work
- Scale to your environment
- Manage cloud computing & shadow IT
- Embed governance in workflows
- Build supply chain resilience
- Extend security policy outside the enterprise
Explore other Mandiant Advantage Modules
Attack Surface Management FAQ
Attack surface management is an approach to cyber defense that assesses and monitors external and internal assets for vulnerabilities as well as any risk that can potentially impact an organization.
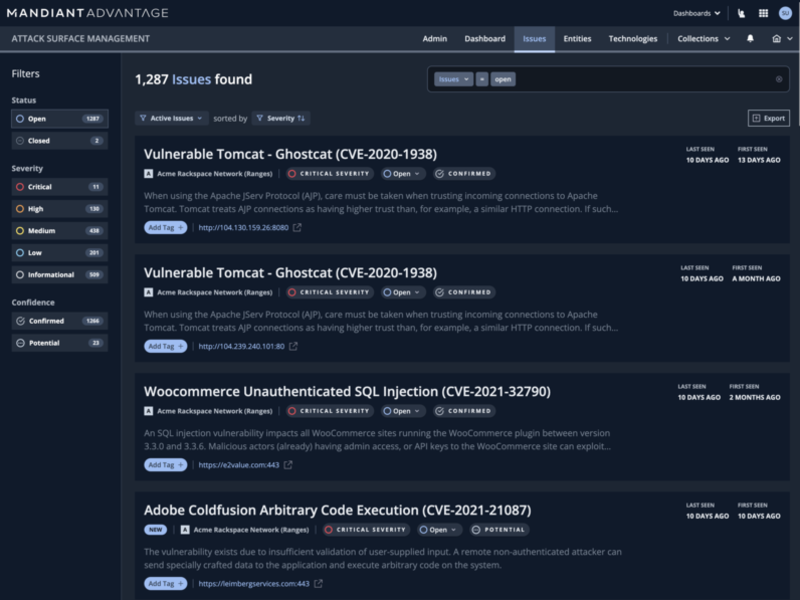
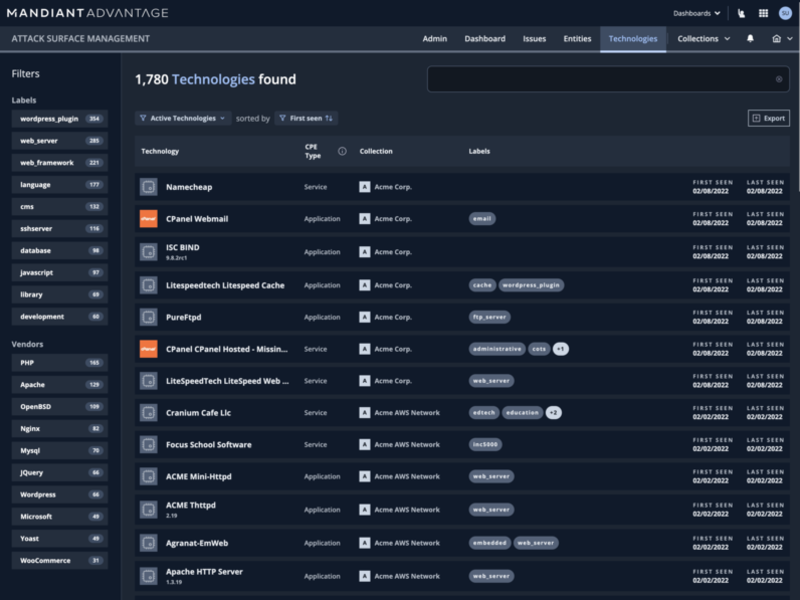
An attack surface management solution continuously discovers and assesses an organization’s assets for vulnerabilities, misconfigurations and exposures.
A distributed work force allows employees to access an organization’s network from anywhere, making it harder to enforce security policies and introducing new risks. A security team can use attack surface management to continuously monitor network access and devices, mitigate risk and enforce appropriate security policies.
An attack vector is an exploitable asset in the attack surface. An attack vector can be used by a threat actor for initial compromise.
To reduce the overall attack surface, attack surface management solutions generate an asset inventory and alert the security team to exposed assets that can be targeted for exploitation.
An external attack surface management solution performs assets and exposure discovery on internet-facing assets. It continuously assesses them for vulnerabilities and generates and prioritizes issues for the security team to remediate.
Examples of attack surfaces include domains, IP ranges, data repositories, websites, servers, email, cloud resources, applications, microservices and employees.
A network’s attack surface includes any application, device or user that can access the network. Examples include network services, hosts and IP ranges.