![]()
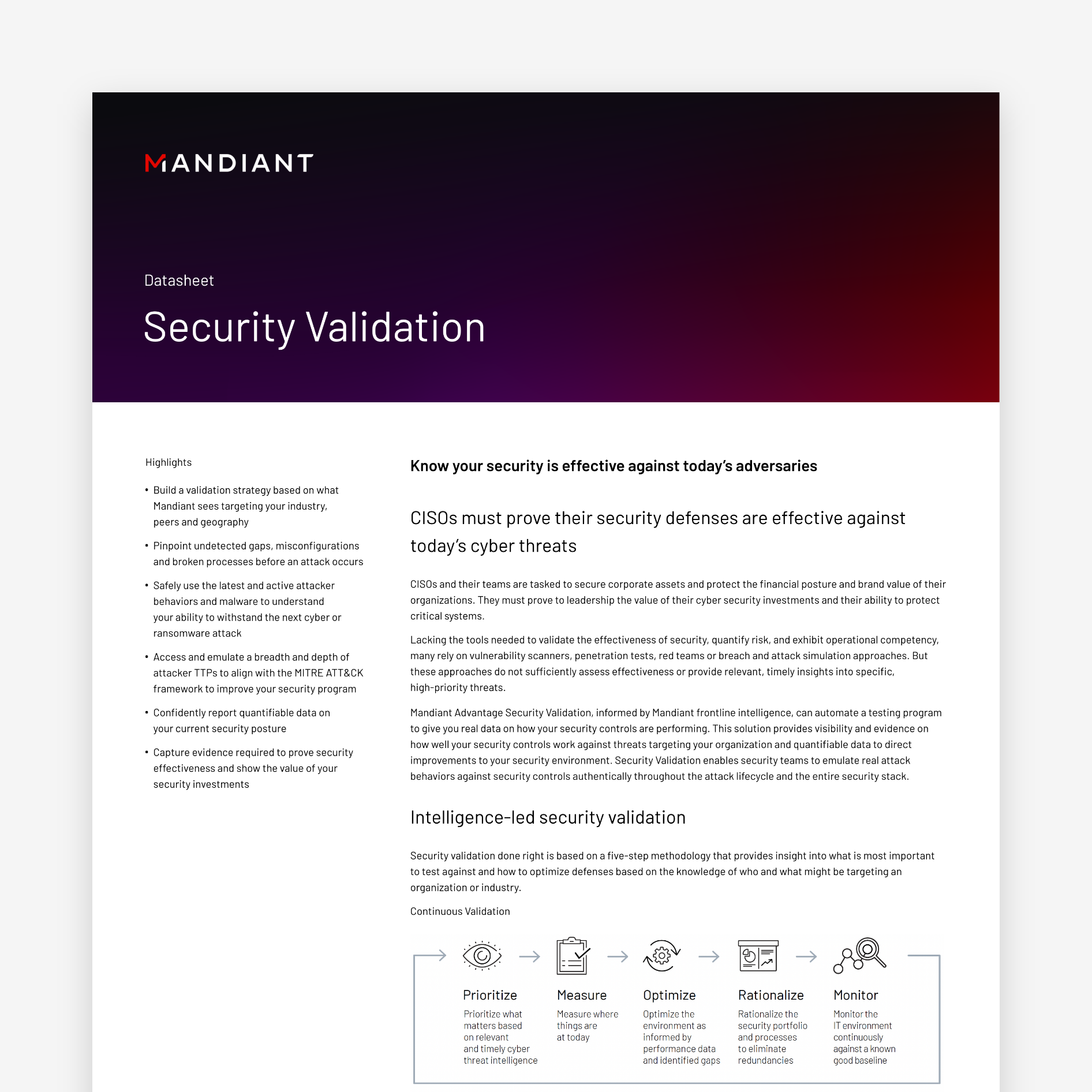
Improve Security Posture Measurement
Learn about your readiness for a potential attack. Use frontline intelligence to assess your cyber defense posture.
![]()
Test your Cyber Defenses
Know if your security tools and processes will effectively protect you against real-world targeted attacks
![]()
Gain Confidence
Are you prepared? Assess, validate and measure your security controls effectiveness
![]()
Assess Risk During Due Diligence
Identify and assess merger and acquisition risk that is outside of your control
![]()
Validate Security Stack Effectiveness
Test and measure the efficacy of your security stack
![]()
Emulate Real-World Attacks
Emulate modern attacker TTPs to validate coverage across the NIST and MITRE ATT&CK frameworks.

The Definitive Guide to Security Validation
Learn about the evolution of security testing and what to consider when using simulation versus actual emulation. Test your current defenses against modern threats.
Validate your security posture
Data, intelligence and expertise help to build and maintain the best cyber defense. Testing your security architecture and processes against real-world, modern-day attacks provides the evidence needed to build your security confidence.
27% of Mandiant incident response investigations uncovered multiple threat groups in the same environment.
Source: M-Trends 2023
73%The likelihood of specific attacker techniques used during an intrusion should impact an organization’s security investment decision-making process.
In 2022, Mandiant observed 73% of MITRE ATT&CK techniques used by adversaries across investigations. This proves the defensive value of prioritizing and validating implementation of the right security measures to protect against the most commonly used techniques.
40%Nearly 40% of intrusions where compromised architecture was observed, resulted in ongoing spam, phishing operations and distribution of botnets.
FAQ
Data captured by security validation enables security teams to identify gaps, misconfigurations, redundancies, lack of accurate SIEM correlation and alerting within a security program and opportunities for continuous optimization and measure of improvement over time.
- Evidence of security effectiveness (security infrastructure health)
- Demonstrated value of security investments (spend rationalization)
- Quantitative reporting to executives and non-technical stakeholders
- Security framework assessments (MITRE ATT&CK Framework or NIST)
- Technology evaluations
- Operationalization of threat intelligence and threat actor assurance
- Advanced malware and ransomware defense validation
- Mergers and acquisitions
- Cloud controls validation
Security Validation is informed by timely threat intelligence and executes automated and continuous testing of security controls with the use of real attacks. Although there are different approaches to testing security effectiveness, the emulation of real attack behaviors and malware against an organization’s security controls and across the entire security stack enable the capture of quantifiable data on how security controls perform under attack. This approach to security validation provides visibility into gaps, misconfigurations and the ability to identify areas for improvement to continuously optimize security defenses against the most relevant threats.
Getting Started
Knowing where to begin can be a challenge. Set up time to tell us what your goals are and a Mandiant expert can help plan how to validate your security controls effectiveness against recent adversaries and TTPs.