“The Defender’s Advantage is a recipient of the prestigious annual Global Infosec Awards from Cyber Defense Magazine (CDM). “
What is The Defender’s Advantage?
As prominent attacks continue to dominate the headlines, security teams are under pressure to detect and respond to malicious activity faster than ever before.
The Defender's Advantage is a concept that organizations are defending against attacks in their own environment, on their own terms.
This provides a fundamental advantage arising from the fact that they have control over the landscape where they will meet their adversaries. Organizations struggle to capitalize on this advantage.
Understanding and activating the six functions of cyber defense help your security organization capitalize on The Defender’s Advantage.
Intelligence
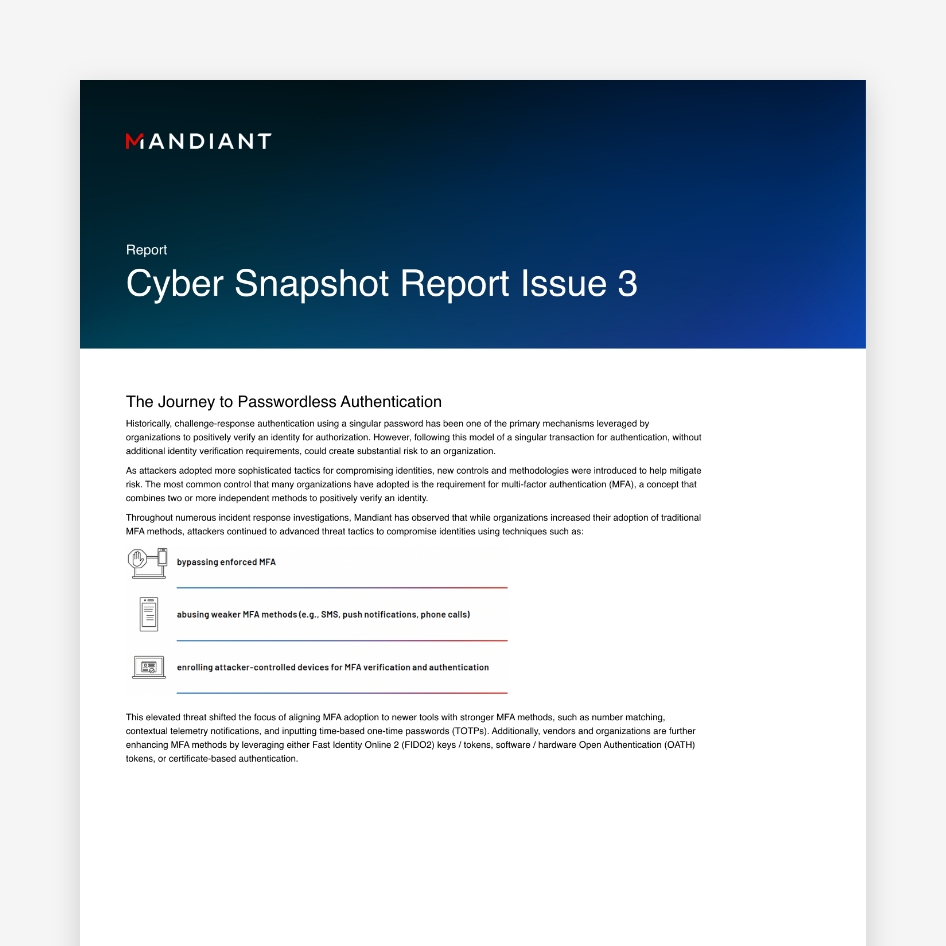
Intelligence guides actions within the cyber defense organization. Its quality, relevance and usability make a huge difference to cyber defense. Most security organizations subscribe to threat intelligence feeds, but they struggle to operationalize it.
Respond
As the Detect and Hunt functions identify suspicious activity, the Respond function confirms if that activity is malicious by understanding the full extent of compromise, minimizing business impact and returning services to normal operations
Hunt
Threat hunting proactively uses intelligence about an adversary and their operations to search for active or previous compromise. Threat hunting is a combination of automated and human-led elements and requires ascribing to the adversary mindset.
Validate
Targeted testing, mission based or objective based testing, and continuous controls validation help validate that security controls are protecting critical assets as intended.
Detect
Detect valid malicious behavior within the environment by identifying critical events among collected alert information. Intelligence guides efficiency so critical events can be prioritized and acted upon.
Command and Control
The Command-and-Control function establishes authority and direction to align each function to the cyber defense mission.
This is likely the best webinar I have ever attended. Super-relevant topic, loved the explanations and methodology shared. If people follow this model, companies will be more secure and effective.
Kimberly Tuttle, Russell Investments
Watch The Defender's Advantage Virtual Series
Watch our four-part webinar series to learn the methodology and best practices surrounding the six critical functions of cyber defense that make up The Defender’s Advantage.
On-Demand Sessions:
- Part 1: Take Control of Your Cyber Defense with The Defender’s Advantage
- Part 2: Utilize Threat Intelligence, Establish Command & Control
- Part 3: Detect Risks & Validate Security Controls
- Part 4: Respond to Resume Operations & Hunt to Prevent Compromise
Let’s work together
Contact us for expert guidance on enhancing your cyber defense.
The Defender’s Advantage Resources
Have questions? Let's talk.
Mandiant experts are ready to answer your questions.